Security Best Practices
Passwords
Tip: Use an 8+ character password with mixed case/numbers/symbols along with 2FA (Two-Factor Authentication)
Passwords are among the first lines of defense to fail. It won’t surprise anyone that the two most commonly used passwords are ‘123456’ and ‘password’. Many of us are afraid to create complex passwords for fear of forgetting them.
The easiest method to harden your password security is to think of at least three 8+ character passwords with mixed case/numbers/symbols. ‘Mentally label’ each of the three passwords as green/yellow/red. Choose the green password for the lowest security sites that have no real personal info — save the red passwords for banking or shopping sites that retain your account numbers and credit cards. As these passwords are used for more and more sites, rotate out your green password and replace it with yellow and red — making them the new green password. Lastly, establish a new red password for your highest security sites.
Even an 8+ character password, though, can be guessed by special hacking computers within 5-6 hours. We must also pair our complex passwords with 2-step verification or 2-factor authentication where a successful login then prompts us to confirm our identity with a code sent to our mobile phone or email address. Google has supported 2-Step-Verification for years and if not already using it for your Google/Gmail accounts, you should enable it immediately.
Any site that holds sensitive information that does not support 2FA, should really be reconsidered as a site you continue using or at least should have a 12 or 15 or 20 character complex password — or better, passphrase such as, “my b1rthplace 1s Cleveland” (include spaces).
Website Security
Tip: Login to websites only if they display a ‘lock’ in the address bar
Websites that require a user to login with an established username and password are responsible for protecting the information they retain — passwords, addresses, credit card info, etc — with a security protocol called SSL. This protocol prevents unauthorized websites to mimic or ‘pose’ as valid sites and also prevents ‘eavesdropping’ of data while traveling between your computer and the site.
You can recognize websites that have established this security certification by looking in the web browser address bar when visiting the site.


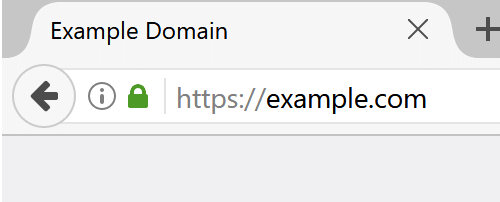
Make it a policy to check for this security ‘lock’ before logging into any website and entering any personal information.
Web Browser
Tip: Use a Standards Compliant Web Browser such as Chrome, Firefox or Safari.
Your continued use of Microsoft’s Internet Explorer may be the cause of your past computer infections. The standards used to deliver web data have been notoriously non-standard when involving Internet Explorer historically. Though recent versions (like Microsoft Edge) have improved, there is little reason to maintain a loyalty to IE. Even if a website recommends its use, consider an alternative website that does NOT require it. Your security may be at risk.
Popular browsers like Chrome, Firefox and Safari allow for plug-ins, or helper programs, to add features and functionality by 3rd party software companies. We recommend adding the HTTPS Everywhere plug-in to your web browser. This plugin enforces the use of SSL or https on websites.

VPNs
Tip: Install a browser based or standalone VPN (Virtual Private Network) service for ~$4/month
Although mostly used by computer techies and foreign dissidents speaking out against their censoring governments, the use of VPNs is gaining attention in today’s security addled climate. This PC Magazine article best describes the function of a VPN and the excerpt below offers a brief summary.
We use and recommend KeepSolid’s VPN Unlimited which is reviewed in the article and selected as an Editor’s Choice.
What Is a VPN?
A VPN is a lot more than just something you need for remotely accessing your work files. When you switch on your VPN, it creates an encrypted tunnel between your computer and the VPN server, which can foil hackers or even government snoops trying to eavesdrop on your activities. From the server, your web traffic travels off into the public internet, but your actual IP address remains hidden. Data-hungry website advertisers see the IP address of the VPN server instead of your own. We recommend using a VPN as often as you can, but especially when your PC is connected to a public Wi-Fi network. When you hop on an unsecured network at the airport or coffee shop, you have no way of knowing whether the network is what it claims to be. Instead of a convenience offered to thirsty customers and weary travelers, the network could have been created by a hacker looking to intercept your data. VPNs can also be used to disguise your actual location, which is why these services are often used by journalists and political activists operating in countries with restrictive internet controls.